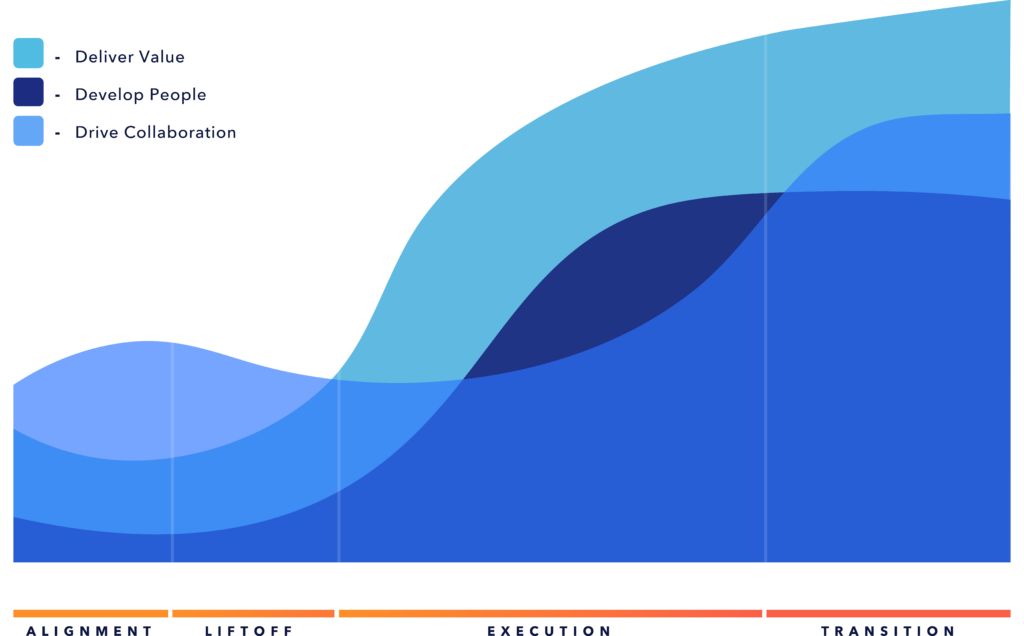
The key to getting FedRAMP authorized
Ensure your path to FedRAMP readiness is built on the solid foundation of organizational design and change, paving the way for a smoother compliance journey and enhanced operational efficiency.
Leveraging the cloud to protect against ransomware

Explore the benefits of cloud providers for data backup, network segmentation, and advanced security measures to protect your business against the increasing threat of ransomware attacks.
Trust comes first in a Zero Trust world
Zero Trust flips traditional enterprise perimeter security. An organization should start the journey by setting clear objectives and direction before heading too far down the path of implementation.
Are new security trends really all that new?
By leveraging design principles, both current and original, that ensure security, teams can continue applying new tools to meet their needs and adapt to constant change while continuing to protect from every threat.
Balancing speed and security with DevSecOps
What if speed and security were not polarities? By reimagining the security process, companies can both move quickly and ensure security, gaining the advantages of both.